// The old way
Copy the Key for Everyone
API keys are like house keys.
Right now, you're making copies
for everyone who needs access.
When someone leaves,
you have to change the locks
& hand out new keys
to everyone else.
// Layr8 Way
Controlling the door
You keep the “only key”.
When someone knocks,
you decide whether to let them in.
Revoke someone's access?
Just stop opening the door for them.
contractor?
all the locks.
to everyone else.
get in anymore.
every entry.
User / Agent
Knocks on the door
Layr8
Checks identity, opens door
Your APIs
REST, MCP, any endpoint
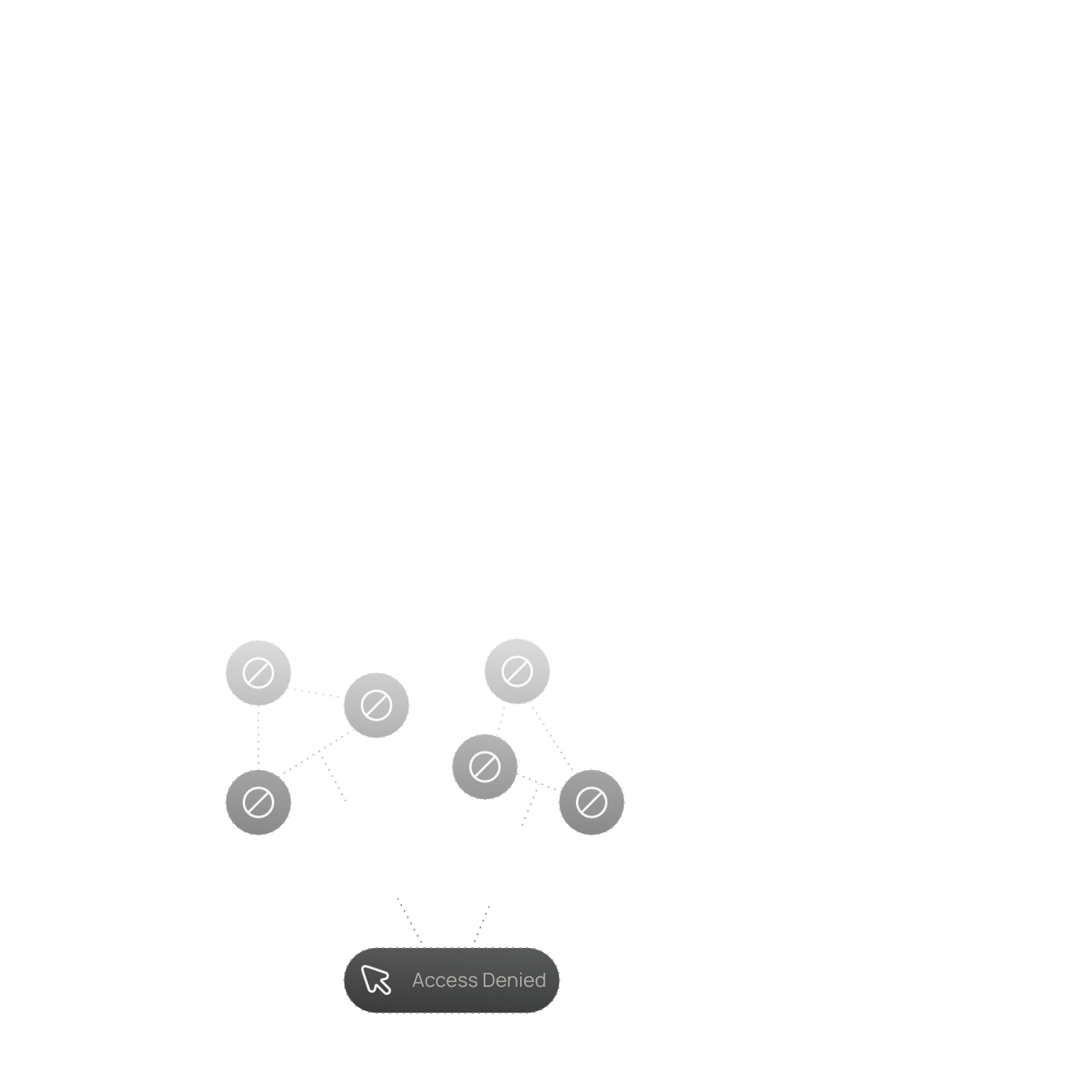
Identity Replaces Keys
The Layr8 Zero-Trust Gateway is an identity-first API security platform. Your credentials are securely managed per-tenant. Users and agents prove who they are—we look at the identity, check if they should have access, and make the API call on their behalf.
Keys Never Leave
Your API credentials are stored securely in your tenant. Contractors, employees, and agents authenticate with identity—they never see or touch the actual keys.
Instant Revocation
Stop opening the door for someone and their access ends immediately. No key rotation. No disruption to anyone else. No guessing.
Full Audit Trail
Every API call logged by identity. Know exactly who or what made each request. Who came through the door, when, and what they did.
Granular Permissions
Control what each identity can access. Some people can enter the living room but not the bedroom. Per user, per agent, per endpoint.
Works With Everything
REST APIs, MCP servers, any HTTP endpoint. If it takes an API key, Layr8 can proxy it. No changes to your existing infrastructure.
Built on DIDs
Decentralized identity (DIDComm) means cryptographic proof of who's knocking. No passwords to steal. No tokens to intercept.
// The Key-Copying Problem
is Getting Worse
API keys are the most common
and most
preventable cause
of
security incidents.
84%
Of security professionals experienced
an
API security incident last year
Source: Akamai Research
70%
Of leaked secrets from 2022
were still active
in 2024
Source: GitGuardian
39 Million
Secrets leaked on GitHub in 2024 alone a 67% increase year-over-year
Source: GitHub Security Report
$4.88M
Average cost per breach involving compromised credentials
Source: IBM Cost of Data Breach
// For Development Agencies
Win Deals by Never Touching Their Keys
Your clients hesitate to hand over production credentials.
What if you could tell them they don't have to?
The Trust Problem
Every client worries about the same thing: "I'm giving a remote team my API keys. What happens when the project ends? What if someone copies them? How do I know what they're doing with them?"
Your New Differentiator
"We're a Layr8 partner. Your credentials never leave your control. You grant access to us, we manage our own team—and you can see every API call we make. Revoke our access anytime with one click."
// How It Works For Partner Agencies
Client Keeps
the Keys
Client Grants
Access to
Your Agency
You Manage
Your Own Team
Your Team Works
Through Layr8
Client Has
Full Visibility
Project Ends,
Access Ends
Your client adds their APIs and credentials
to Layr8.The keys stay with them—always.
Your client adds their APIs and credentials to Layr8.
The keys always stay with them.
The client trusts your agency as an entity and sets the boundaries—which APIs what permissions, read-only or write access.
The client trusts your agency as an entity and sets the boundaries—which APIs, what permissions, read-only or write access.
As a Layr8 partner, you issue DIDs to your developers.
Onboard new team members, offboard when they leave.
The client doesn't manage individual identities.
As a Layr8 partner, you issue DIDs to your developers. Onboard new team members, offboard when they leave.
The client doesn't manage individual identities.
Developers authenticate with their identity and make API calls through the proxy. Full functionality, zero key exposure.
Developers authenticate with their identity and make API calls through the proxy. Full functionality, zero key exposure.
Every request logged by identity. Client sees exactly
what your team accessed, when, and what they did.
Complete transparency without the management burden.
Every request logged by identity. Client sees exactly what your team accessed, when, and what they did. Complete transparency without the management burden.
Client revokes your agency's access—one action.
All your team members lose access instantly.
No key rotation. No loose ends.
Client revokes your agency's access-one action. All your team members lose access instantly. No key rotation. No loose ends.
Ready to win
more deals
with security as
your differentiator?
A ready-made deck you can use when pitching
security-conscious clients
Win more deals
Write to Layr8 once.
Connect to any partner on the mesh.
Reduce your liability
Both sides verify.
No spoofing. No drift.
Prove your work
Access by identity and policy —
not exchanged credentials.